What does vendor management under HIPAA really require?
HIPAA requires healthcare organizations to evaluate the risk that vendors pose to protected health information (PHI), ensure that vendors meet security and privacy requirements (including executing a Business Associate Agreement), and document these efforts as part of their ongoing compliance and risk management programs.
Why Vendor Management Matters Under HIPAA
In the world of HIPAA compliance, your vendors can make or break your risk posture.
Business associates, cloud platforms, EHR vendors, billing services, email providers, etc. often hold or process PHI on your behalf. Under the HIPAA Security Rule (45 CFR §164.308(b)), you are required to obtain satisfactory assurances that these vendors will safeguard PHI appropriately.
But it’s not just about paperwork. OCR investigations routinely probe vendor vetting practices, not just the BAA itself. In some enforcement cases (Care New England Health System), regulators noted that the provider “failed to timely enter into a business associate agreement” before allowing access to PHI.
That’s a preventable and expensive mistake.
Depth: What to Collect, How to Score Risk, and How to Prove It
1. What to Collect from Each Vendor
A strong HIPAA vendor management process starts with documentation. At a minimum, collect:
- Business Associate Agreement (BAA) – Signed before PHI access begins. Clearly outlines permitted uses, safeguards, and breach notification timelines.
- Security Questionnaire or Due Diligence Form – Ask about encryption, access controls, breach history, audit logs, subcontractor use, etc.
- SOC 2, HITRUST, ISO 27001 Reports (if available) – These third-party audits can reduce your assessment burden.
- Evidence of HIPAA Training and Workforce Controls – Especially for vendors who will directly handle PHI.
- Contact Information for Incident/Breach Reporting – You must know who to call if something goes wrong.
- Risk Categorization (High, Moderate, Low) – Based on volume/sensitivity of PHI and access level.
Optional but helpful: vendor W-9, business license, data flow diagrams, API documentation, and support escalation procedures.
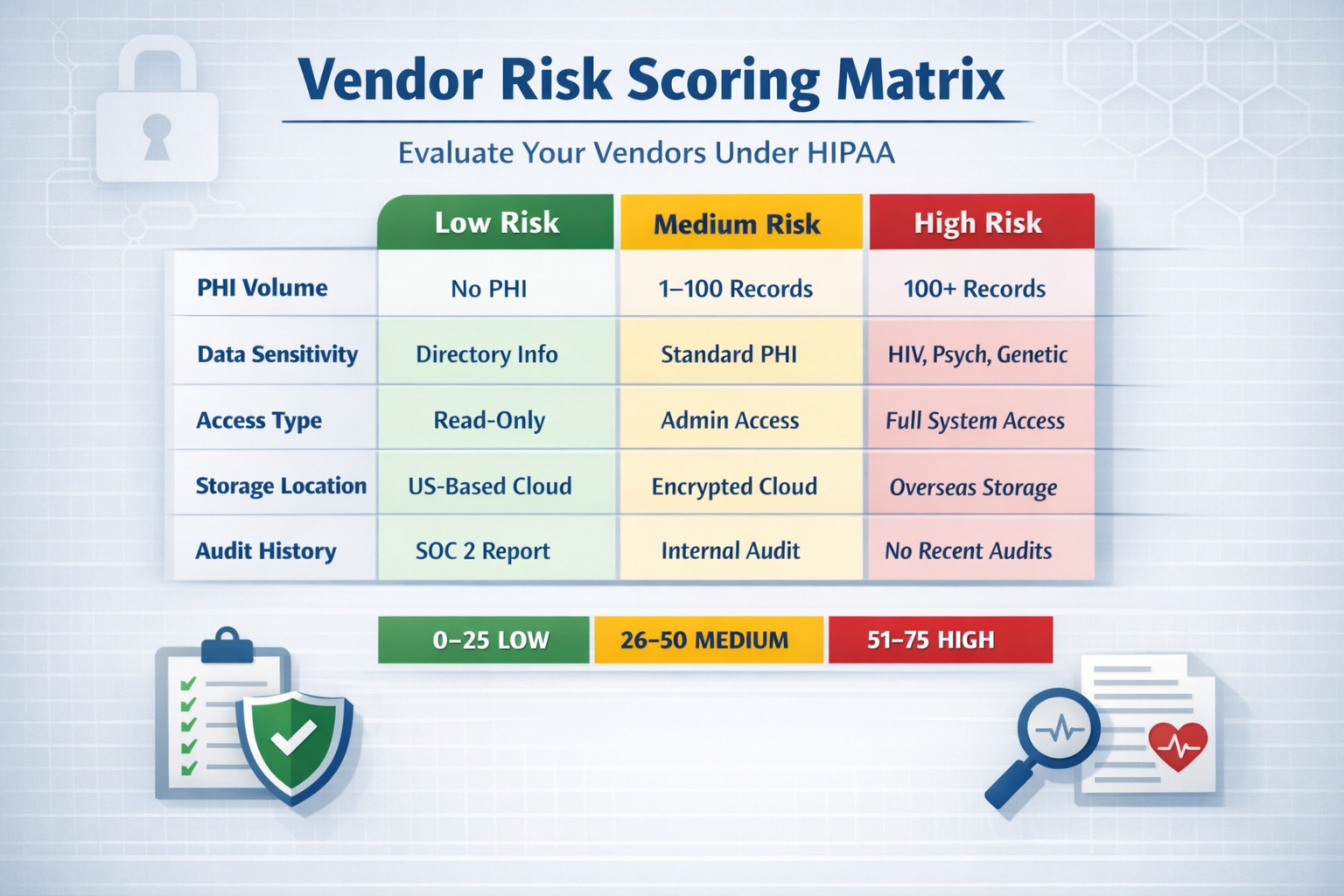
2. How to Score Vendor Risk
Use a consistent and repeatable scoring system to prioritize review efforts. Here’s a sample risk matrix:
| Risk Area | Low | Medium | High |
|---|---|---|---|
| PHI Volume | No PHI | 1–100 records | 100+ records |
| PHI Sensitivity | Directory Info Only | Standard PHI | HIV, Psych, Genetic, Substance Use |
| Access Type | Read-Only | Admin UI Access | System-Level or API Write Access |
| Storage Location | No storage | Encrypted Cloud with US Storage | Unclear or International Cloud Storage |
| Third-Party Subprocessors | None | Disclosed with Controls | Undisclosed / High Volume Subprocessors |
| Audit History | SOC 2 or HITRUST | Internal audit only | No audits or refused to share |
Then assign a weighted score and rank vendors accordingly (0–25 = Low Risk, 26–50 = Medium Risk, 51–75 = High Risk).
3. How to Prove It to Auditors or OCR
HIPAA doesn’t just ask you to do the work, it asks you to prove it. Here’s how to turn your vendor management program into defensible documentation:
- Maintain a Vendor Inventory Log – Include risk ratings, BAA status, last review date, and primary contact.
- Retain Copies of All BAAs – Archive signed BAAs with version control and effective dates.
- Keep Due Diligence Records – Store questionnaires, risk scores, review notes, and vendor responses.
- Document Review Frequency – Set a review cadence (annually for high-risk, bi-annually for low-risk) and log each review.
- Log Vendor Breach Events – If a vendor has a security incident, document when/how they notified you and your response.
- Use a Centralized Platform – Systems like Medcurity or OneTrust can streamline documentation, alerts, and evidence tracking.
Pro Tip: If OCR audits your organization, they often ask: “How do you know your vendors are HIPAA-compliant?” Your ability to produce a current, dated risk assessment and due diligence documentation is often the difference between passing and paying.
In Conclusion: Vendor Risk is Your Risk
Under HIPAA, you’re not just responsible for your internal practices, you’re on the hook for your vendors, too. A signed BAA is not enough. You need a structured, repeatable process to evaluate risk, assign accountability, and track changes over time; the good news, you don’t need to do it manually. Platforms like Medcurity offer pre-built BAA templates, vendor inventory tools, and smart risk scoring. Compared to spreadsheets or outdated BAA binders, modern vendor management tools reduce liability and make it easier to prove you’re doing the right thing. Your vendors hold your patient trust. Treat their risk like it’s your own, because it is.




Leave a Reply